Not just another Kafka UI
KafkaKombat is aimed at Kerberos-only environments where a Kafka UI must respect the real access model instead of bypassing it
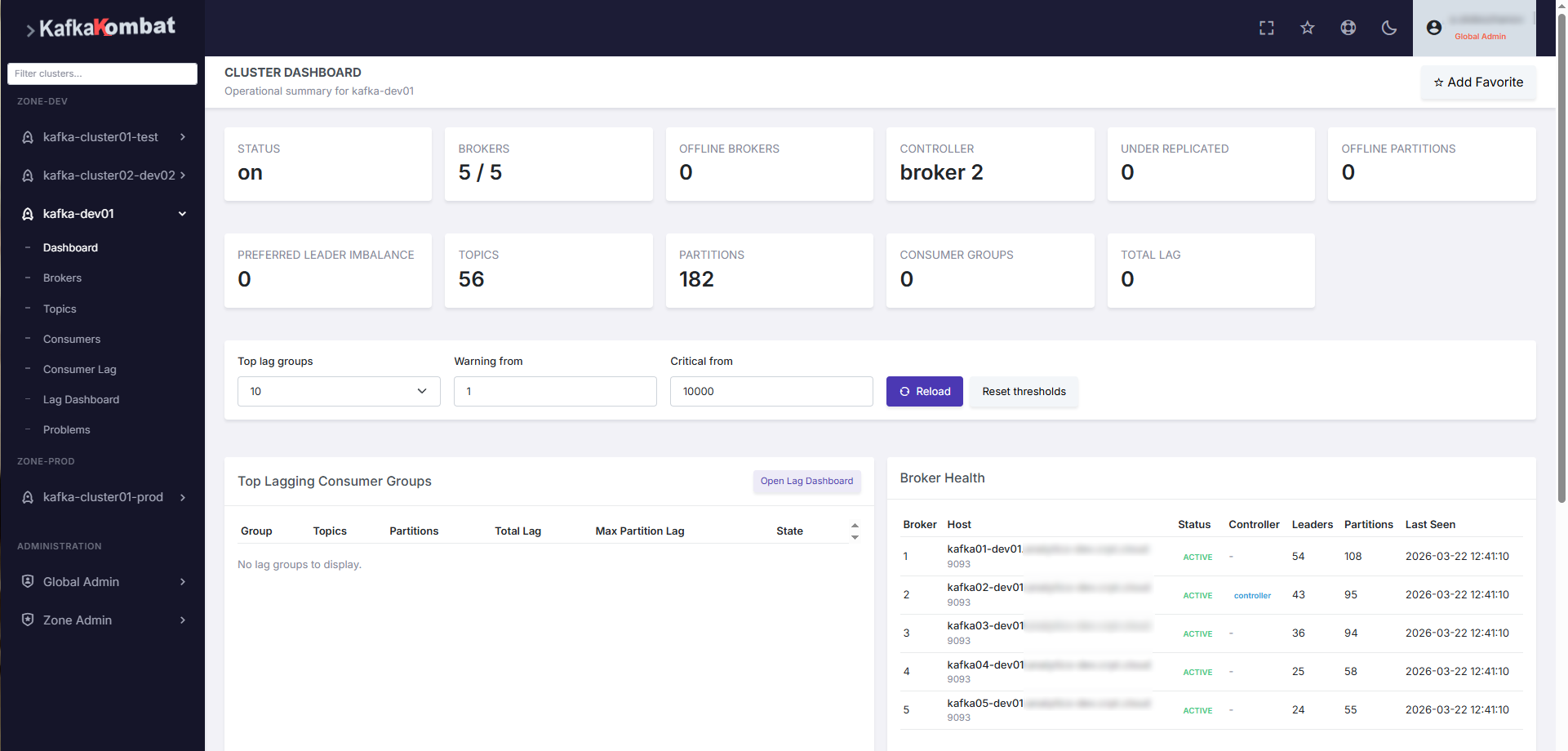
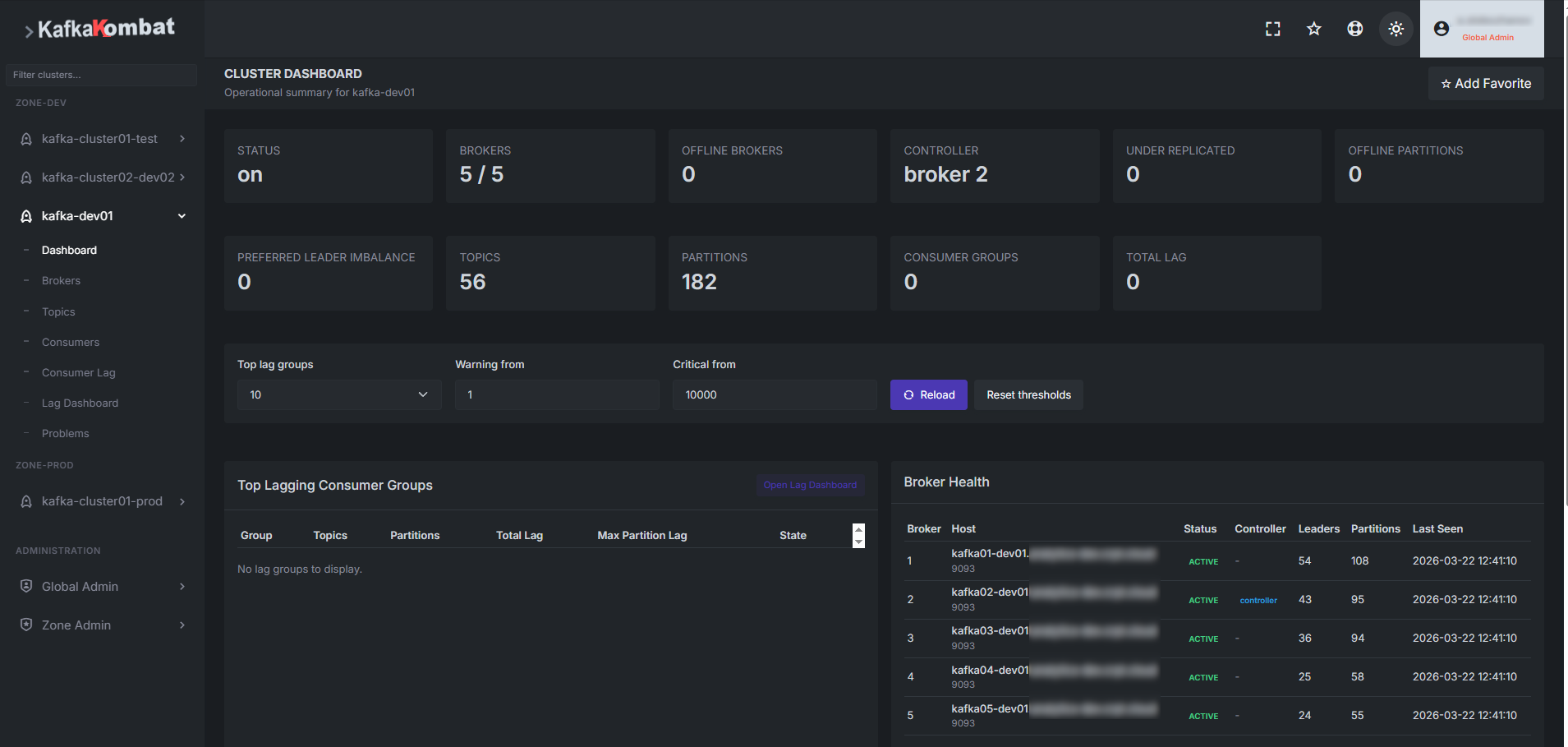
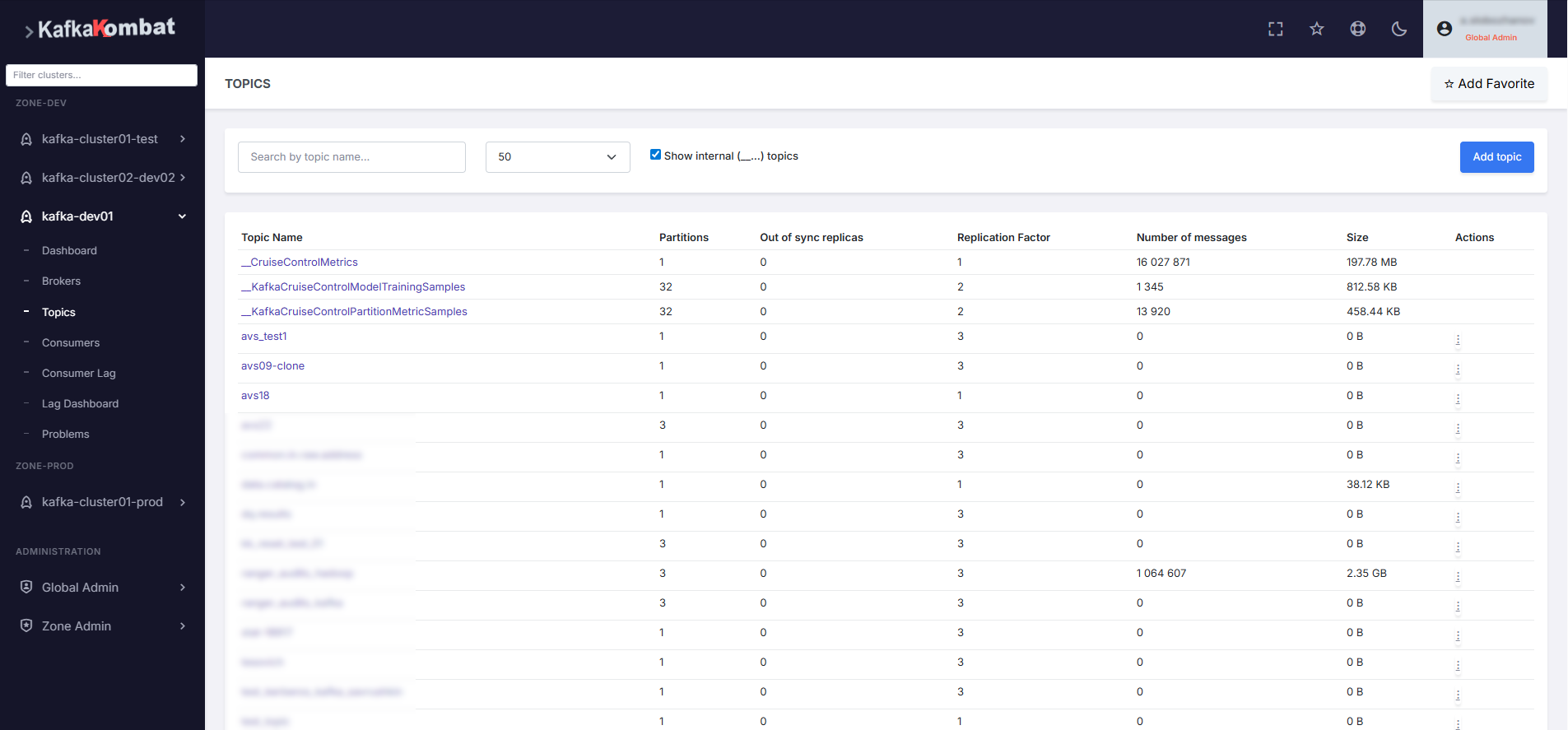
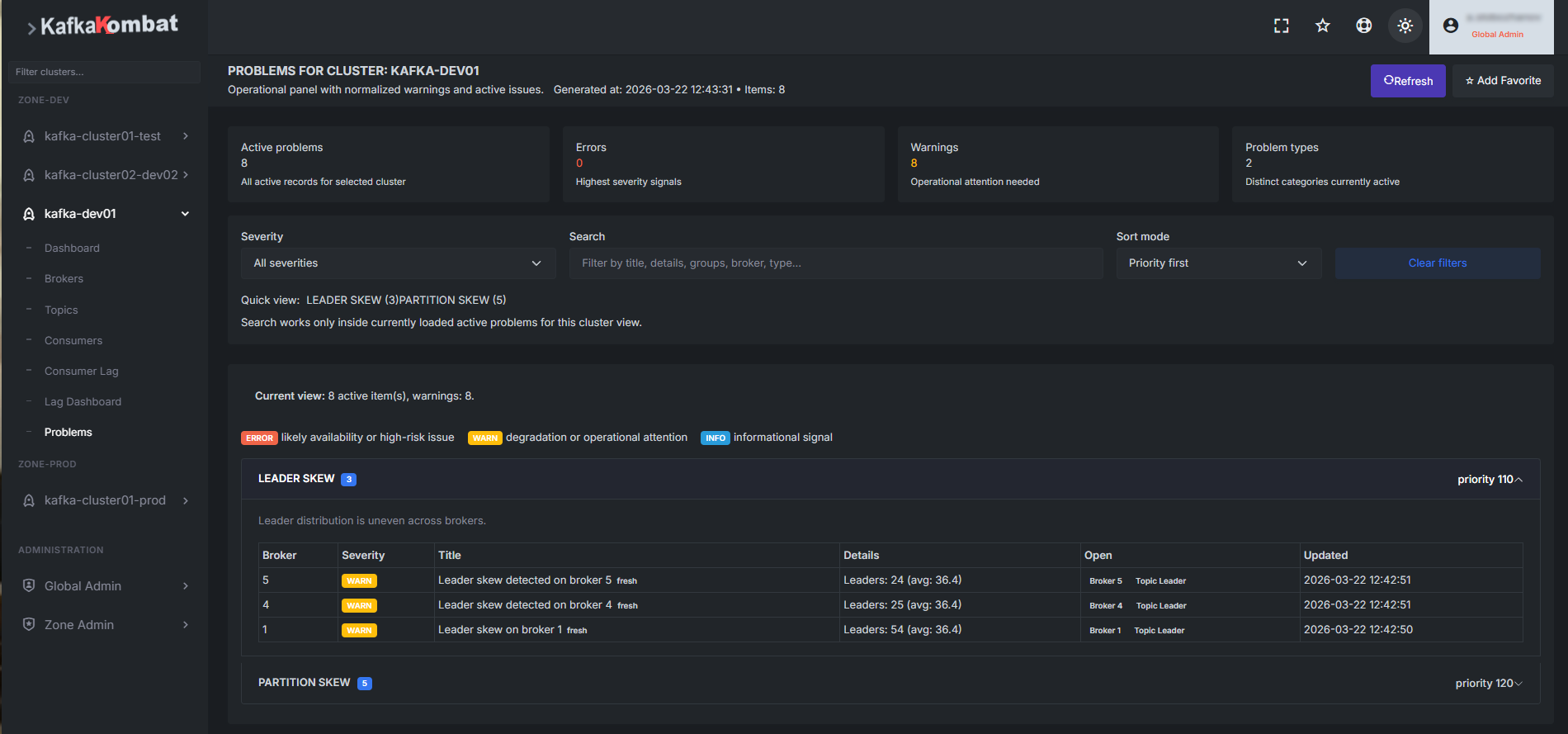
KafkaKombat is a free Kerberos-first web UI for Apache Kafka. It is built for Kafka environments where SASL/GSSAPI, centralized roles, access zones, secure message browsing, and controlled administrative operations are part of the real production model rather than optional extras. A key difference of the product is that normal UI-driven Kafka requests are executed with the user’s own Kerberos ticket instead of a shared service identity
KafkaKombat is aimed at Kerberos-only environments where a Kafka UI must respect the real access model instead of bypassing it
One installation can work with multiple Kafka clusters grouped into access zones with Global Admin, Zone Admin, and application RBAC
The current line is already distributed free of charge as a Linux server distribution and as a Helm chart baseline for Kubernetes. The project is planned to move to Open Source starting with the 2.2 line
KafkaKombat is designed for Apache Kafka environments where Kerberos and SASL/GSSAPI are part of the normal client runtime, including krb5.conf, ticket cache handling, and production-grade Kafka authentication
Normal UI actions are executed with the Kerberos ticket of the logged-in user. Service principal and keytab are reserved for backend and background functions rather than replacing the user for everyday UI operations
The product is already used in development and production environments by multiple internal teams working with Kerberos-protected Apache Kafka clusters and a multi-cluster operational model
KafkaKombat has been tested with Apache Kafka versions 3.0.0 through 4.2.0. If support for additional Kafka versions is required, feedback and issue reporting channels are available through the website and GitHub
The server distribution and Helm chart are both available free of charge today
The project can be deployed in two basic ways: as a Linux server distribution and as a Helm chart baseline for Kubernetes. The Helm chart is intentionally published as an environment-neutral baseline and is expected to be adapted to the target infrastructure
Environment requirements, quick start, and installation options
Public-facing product and installation documentation for evaluation and rollout
Current stable release, published artifacts, checksums, and signature metadata
GitHub, roadmap, private security contact, and project status